Papers That Shaped Fully Homomorphic Encryption Research and Development
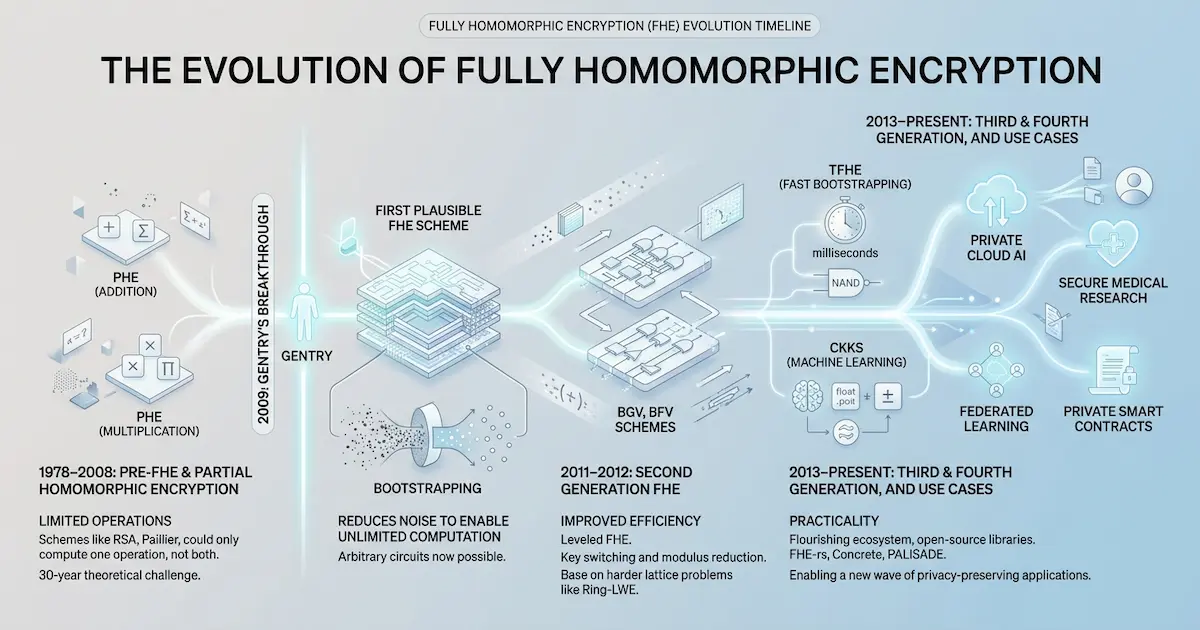
The evolution of Fully Homomorphic Encryption (FHE) is one of the most fascinating arcs in modern cryptography. It transitioned from a theoretical “holy grail” that many believed was impossible, to a practical engineering discipline currently reshaping privacy-preserving computation, machine learning, and decentralized infrastructure.
This list curates seminal papers not just for their citation count, but for their contribution to the engineering feasibility and architectural paradigm shifts of FHE—from the first existence proof to the modern era of hardware acceleration and verifiable blockchain integration.
Introduction
For decades, the ability to compute on encrypted data was purely theoretical. The dream was simple: allow a third party to process data without ever seeing it. But for a long time, the “FHE overhead”—often millions of times slower than plaintext—made it an academic curiosity rather than an engineering tool.
Today, that reality has inverted. Thanks to algorithmic breakthroughs like “programmable bootstrapping” and the arrival of dedicated hardware accelerators, FHE is crossing the chasm from “mathematically possible” to “commercially viable.” We are no longer asking if it works, but how to architect systems that integrate it.
The following sections track the Epochs of FHE research, marking the journey from the first existence proof to the current era of confidentiality-preserving blockchains and encrypted AI training.
Epoch 0: The Genesis & Existence Proof
Transitioning from theoretical impossibility to the first working cryptographic construction.
1. On Data Banks and Privacy Homomorphisms (1978)
Paper: On Data Banks and Privacy Homomorphisms (1978)
This paper was the first to conceptualize FHE. Shortly after inventing RSA, Rivest, Adleman, and Dertouzos asked whether it was possible to create a “privacy homomorphism”—an encryption scheme allowing complex computations on encrypted data without decryption. It set the target for the next 30 years of cryptographic research.
For developers, this is the “seminal question” that shifted the cryptographic mindset from simply hiding data (encryption at rest/transit) to computing on hidden data (encryption in use). It established the “Holy Grail” of cryptography.
2. Fully Homomorphic Encryption Using Ideal Lattices (2009)
Paper: Fully Homomorphic Encryption Using Ideal Lattices (2009)
This is the watershed moment. Craig Gentry provided the first working FHE scheme using ideal lattices. His critical contribution was bootstrapping—a method to periodically “refresh” a ciphertext to reduce the noise accumulating during operations. Before this, schemes were limited to a finite depth (Somewhat Homomorphic Encryption); Gentry proved unlimited computation was possible.
This was the “Hello World” moment. While impractical for real-world use, Gentry proved that noise—the primary adversary in FHE—could be managed algorithmically, turning FHE from a mathematical impossibility into an engineering optimization challenge.
3. Fully Homomorphic Encryption over the Integers (2010)
Paper: Fully Homomorphic Encryption over the Integers (2010)
Following Gentry’s breakthrough, this work simplified the construction by using integers instead of ideal lattices. It demystified the underlying mechanics, making FHE accessible to the broader cryptographic community.
From an engineering perspective, this lowered the barrier to entry. It demonstrated that FHE didn’t require exotic math, just very large integers, making the schemes easier to audit, understand, and implement in standard software environments.
Epoch 1: Efficiency & LWE Foundations
Moving from impractical ideal lattices to efficient, quantum-resistant LWE/RLWE schemes.
1. Fully Homomorphic Encryption without Bootstrapping (BGV) (2012)
Paper: Fully Homomorphic Encryption without Bootstrapping (2012)
Gentry’s original scheme was theoretically beautiful but practically slow. BGV introduced “modulus switching” to manage noise growth more effectively. It proved that one could build highly efficient “Leveled” FHE schemes (evaluating circuits up to a fixed depth) based on the Learning With Errors (LWE) problem.
This marked the birth of “Leveled FHE.” Developers could now trade infinite depth for raw performance. For use cases with fixed-depth logic (like database queries or statistical averages), BGV remains a dominant choice due to its efficient SIMD (Single Instruction, Multiple Data) batching capabilities.
2. Somewhat Practical Fully Homomorphic Encryption (BFV) (2012)
Paper: Somewhat Practical Fully Homomorphic Encryption (2012)
Building on BGV, the BFV scheme optimized arithmetic operations by removing the complex “modulus switching” step during multiplication. It provided a cleaner, more robust approach to exact integer arithmetic.
For practitioners, BFV is often the go-to for exact integer arithmetic. Its simpler noise management makes it easier to implement and tune, establishing BGV and BFV as the “standard library” for applications requiring precise financial or database operations.
Epoch 2: Fast Bootstrapping & Boolean Circuits
Solving the bootstrapping bottleneck to enable arbitrary-depth logic gate computation.
1. Homomorphic Encryption from Learning with Errors (GSW) (2013)
GSW flattened the ciphertext structure into matrices, replacing complex key-switching with simpler matrix operations. This drastically reduced noise growth asymmetry and laid the mathematical groundwork for fast bootstrapping.
This was a structural paradigm shift. By simplifying the data structure, GSW enabled the “control flow” of homomorphic operations to become far more manageable, directly enabling the “Fast Bootstrapping” revolution that followed.
2. FHEW: Bootstrapping in Less Than a Second (2015)
Paper: FHEW: Bootstrapping Homomorphic Encryption in less than a second (2015)
FHEW demonstrated that instead of large integer circuits, one could evaluate standard boolean gates (NAND) and bootstrap after every single gate in under a second. This made arbitrary-depth boolean circuits practical.
This was the speed breakthrough. It opened the door for “Boolean FHE”—treating ciphertexts as bits in a logic gate. Developers no longer needed to pre-calculate circuit depth; they could run “infinite” loops of boolean logic, albeit slowly.
3. TFHE: Fast Fully Homomorphic Encryption over the Torus (2016)
Paper: Faster Fully Homomorphic Encryption: Bootstrapping in less than 0.1 Seconds (2016)
TFHE optimized FHEW by operating over the Torus (real numbers modulo 1), bringing bootstrapping down to milliseconds. Crucially, it introduced Programmable Bootstrapping (PBS)—the ability to evaluate a table lookup for free during the noise-cleaning process.
TFHE is the engine of modern FHE. For developers, PBS meant that non-linear functions (like ReLU or Sigmoid in neural networks) were no longer expensive approximation bottlenecks but “free” side effects of noise management. This unique feature makes TFHE the standard for exact, bit-wise, and non-linear applications today.
Epoch 3: The Approximate Arithmetic Era (CKKS)
Adapting cryptographic primitives for the continuous values of Data Science and Machine Learning.
1. Homomorphic Encryption for Arithmetic of Approximate Numbers (CKKS) (2017)
Paper: Homomorphic Encryption for Arithmetic of Approximate Numbers (2017)
As AI boomed, the need to encrypt continuous data (like sensor readings or model weights) grew. CKKS introduced “approximate arithmetic,” treating cryptographic noise as standard floating-point error. This alignment allowed FHE to support the complex/real number arithmetic native to data science.
CKKS bridged Cryptography and Data Science. It allowed engineers to port standard machine learning models directly to the encrypted domain without fighting the rigid constraints of exact modular arithmetic, effectively bringing FHE to the NumPy/PyTorch crowd.
2. RNS-CKKS: Optimization for Standard Hardware (2018)
Paper: A Full RNS Variant of Approximate Homomorphic Encryption (2018)
Original CKKS required multi-precision arithmetic, which is slow on standard CPUs. This variant used the Residue Number System (RNS) to decompose large numbers into machine-word-sized integers, enabling the use of efficient Number Theoretic Transforms (NTT).
This was pure engineering optimization. It allowed FHE libraries to leverage native 64-bit CPU instructions and vectorization (AVX-512), unlocking massive performance gains for all subsequent CKKS implementations.
3. Bootstrapping for Approximate Homomorphic Encryption (2018)
Paper: Bootstrapping for Approximate Homomorphic Encryption (2018)
This work introduced practical bootstrapping for CKKS, transforming it from a “leveled” scheme (limited depth) to a “fully homomorphic” one.
This unlocked “Deep” Learning. Before this, CKKS was limited to shallow networks. Bootstrapping enabled the evaluation of deep neural networks (DNNs) where multiplicative depth far exceeds the capacity of a single parameter set.
Epoch 4: Practical Libraries & Compilers
Bridging the gap between cryptographers and application developers through robust tooling.
1. Microsoft SEAL (2016)
Paper: Simple Encrypted Arithmetic Library - SEAL v2.1 (2016)
Microsoft’s SEAL was the first industrial-grade library to implement BFV and CKKS. It prioritized code quality, documentation, and usability over pure academic novelty.
SEAL prioritized “Developer Experience.” It moved FHE from obscure research code (often lost after publication) to a stable dependency (C++/.NET) that enterprises could actually build on.
2. OpenFHE: The Unified Standard (2022)
Paper: OpenFHE: Open-Source Fully Homomorphic Encryption Library (2022)
OpenFHE unified major schemes (BGV, BFV, CKKS, FHEW, TFHE) into a single C++ framework. Its killer feature is Scheme Switching, allowing applications to toggle between CKKS (for heavy arithmetic) and FHEW/TFHE (for precise comparisons).
Scheme Switching is an architectural game-changer. It solves the “comparison bottleneck” in approximate schemes, allowing architects to design hybrid circuits that use the best tool for each part of the computation.
3. Orion: The Compiler Era (2025)
Paper: Orion: A Fully Homomorphic Encryption Framework for Deep Learning (2025)
Orion represents the frontier of FHE compilers. It automates the agonizingly complex parameter selection and circuit optimization required for Deep Learning, supporting models like ResNet-50 and YOLO out of the box.
Orion abstracts away the cryptography. It allows ML engineers to focus on model architecture while the compiler handles the translation to polynomial arithmetic. This is the “GCC moment” for FHE—where developers stop writing assembly (manual circuit wiring) and start writing high-level code.
Epoch 5: Privacy-Preserving Machine Learning
Advancing from simple MNIST inference to production-scale encrypted Deep Learning.
1. CryptoNets (2016)
Paper: CryptoNets: Applying Neural Networks to Encrypted Data (2016)
The “Hello World” of encrypted Deep Learning. It demonstrated the first practical neural network inference (MNIST) over encrypted data.
It defined the “ML as a Service” privacy model. It proved that cloud providers could run inference on client data without ever seeing the inputs, setting the architectural pattern for secure AI.
2. Programmable Bootstrapping (2021)
Paper: Programmable Bootstrapping Enables Efficient Homomorphic Inference (2021)
This work formalized the use of TFHE’s bootstrapping to evaluate arbitrary non-linear functions (Look-Up Tables) during the noise refresh.
It turned a maintenance cost into a compute feature. For developers, this meant that the most expensive part of the circuit (bootstrapping) could also perform the most difficult part of the computation (activation functions), streamlining the inference pipeline.
3. ReBoot: Encrypted Training (2025)
Paper: ReBoot: Encrypted Training of Deep Neural Networks with CKKS Bootstrapping (2025)
While inference is useful, training on encrypted data is the holy grail for data privacy. ReBoot demonstrated practical training of DNNs using CKKS bootstrapping.
Training is the “Final Boss.” This work moves encrypted training from “impossible” to “expensive but doable,” paving the way for true Federated Learning where the global model learns from encrypted updates without ever decrypting them.
Epoch 6: Hardware Acceleration
Overcoming the performance gap through dedicated silicon and GPGPU innovation.
1. F1: The First FHE ASIC (2021)
Paper: F1: A Fast and Programmable Accelerator for Fully Homomorphic Encryption (2021)
F1 was the first fully programmable ASIC designed for FHE, outperforming software by 5000x.
It proved the “Hardware Mismatch” theory. FHE wasn’t inherently too slow; it was just running on the wrong hardware. F1 signaled the start of the “FHE Hardware Arms Race.”
2. TensorFHE: GPU Acceleration (2023)
Paper: TensorFHE: Achieving Practical Computation on Encrypted Data Using GPGPU (2023)
TensorFHE demonstrated how to repurpose NVIDIA Tensor Cores for FHE operations.
For the average developer, this is accessibility. You don’t need a custom ASIC; you just need a cloud GPU. It bridged the gap between specialized hardware and commodity cloud infrastructure.
3. FAST: Sub-2ms Latency (2025)
Paper: FAST: An FHE Accelerator for Scalable-parallelism with Tunable-bit (2025)
FAST achieved bootstrapping latency of 1.38ms, bringing FHE performance within striking distance of plaintext for real-time applications.
The “Overhead” is vanishing. For system designers, sub-2ms latency means FHE can finally participate in real-time request/response loops, moving beyond offline batch processing.
Epoch 7: Verifiable FHE & Blockchain Integration
Establishing decentralized trust and composability for privacy-preserving protocols.
1. fhEVM: Confidential Smart Contracts (2023)
Project: FHEVM: Confidential EVM Smart Contracts
Talk: fhEVM: Confidential EVM Smart Contracts using Fully Homomorphic Encryption
fhEVM integrated FHE into the Ethereum Virtual Machine, allowing smart contracts to manage encrypted state.
This is the “Application Layer” breakthrough for Web3. It solves the “Transparency Paradox”—where blockchains require public data for verification. fhEVM proved you can have public verification and private state, enabling “Dark Pools” and confidential voting on-chain.
2. Towards Verifiable FHE (2024)
When you offload FHE to a node, how do you trust it? This paper demonstrated generating a Zero-Knowledge Proof (SNARK) for a TFHE bootstrap execution.
This closes the “Trust Gap.” It ensures that a malicious node cannot return a tampered result. It is the cryptographic glue that allows FHE to run safely on untrusted decentralized networks.
3. FHEVM Whitepaper: The Infrastructure of Privacy (2025)
Whitepaper: fhEVM: Confidential EVM Smart Contracts using Fully Homomorphic Encryption (2025)
This comprehensive whitepaper detailed the production infrastructure for decentralized FHE: offloading symbolic execution to asynchronous coprocessors and using MPC (Multi-Party Computation) for Threshold Key Management.
This moves beyond “Algorithm” to “Architecture.” It lays out the blueprint for a scalable, interoperable FHE network, defining how keys are managed and compute is scaled—effectively designing the “HTTPS” layer for the decentralized web.
Conclusion
The journey from Rivest’s 1978 question to today’s verifiable, hardware-accelerated FHE represents one of computer science’s greatest triumphs. We have moved from asking “is it possible?” to “how fast can we make it?”
As we enter Epoch 7, the focus shifts from pure cryptography to system integration. The challenge for the next generation of engineers is not just optimizing multiplication depth, but building the compilers, coprocessors, and verification layers that will make FHE the invisible standard for the next generation of the internet.